8 Practical data migration validation best practices
Did you know that a staggering 83% of data migration projects either fail or overshoot their budgets and timelines? Don’t be one of them.

Did you know that 83% of data migration projects either fail or exceed their budgets and schedules?
Having data migration validation protocols in place can mitigate these risks. Data migration validation ensures the successful transfer of data from an old system to a new system. It’s an essential process to authenticate the migrated data’s quality, accuracy, and integrity. Whether you’re a seasoned data professional or embarking on your first migration project, this guide will arm you with the best practices you need for an error-free and seamless data transition.
1. Determine the scope of the data migration project
Well before the actual data migration begins, it is vital to determine the overall scope of the migration project and align its objectives with the stakeholders’ expectations. This could include deciding on the migration approach, i.e., big bang or trickle migration. It could additionally involve drafting a requirements specification for the resources needed to carry out the migration process.
Establishing a realistic migration timeline also comes under scoping and provides a structured framework for keeping the project on track. The migration process should maintain existing business operations, but, at the same time, there should be enough room for unexpected delays and rescoping migration goals, if needed. Moreover, relevant metrics and KPIs can be defined in this phase to evaluate the project’s success later on. For instance, this could include tracking the completeness and accuracy of the migrated data, percentage of datapoints successfully migrated, system performance and response times during migration, and costs incurred among other measurements.
2. Perform vigilant assessment of migration infrastructure
Assessing the source system is one of the foundational data migration best practices. This typically includes evaluating various resources such as compute, storage, and network traffic across the source, staging, and destination environments. A thorough assessment of workloads and infrastructure can help companies better understand the capacities and architectural dependencies of the source and target systems.
Migration assessment could involve evaluating data engineering pipelines to ensure efficient data mobility during transition. The existing network infrastructure can also be assessed in detail to have the required connections before the migration. From an assessment of the architectural dependencies, you can then help formulate an effective migration plan.
3. Analyze the source system
Conducting a comprehensive cleansing and analysis of the source data before forwarding it to the migration flows is crucial. Pre-migration validation and data profiling techniques are useful to understand the source data structure better and identify any anomalies and inconsistencies.
Removing inaccurate and outdated information from the source system can help maintain the migrated datasets’ overall data quality. This audit also helps minimize the risk of error propagation during the migration process and ballooning into data redundancy. Plus, by carefully looking at the data before moving it, we can figure out the best way to transfer it.
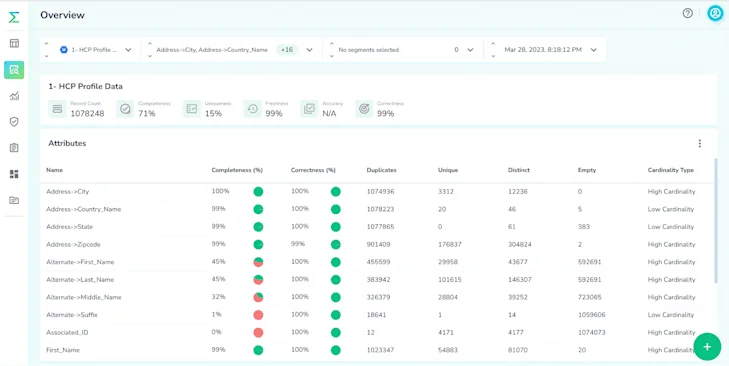
Telmai offers automated profiling, analysis, and outlier detection to help organizations better understand their data architectures before migration. The screenshot above highlights Telmai’s in-house product measuring row-counts and the overall completeness and correctness of the data. For each individual schema attribute, it also looks into the number of unique, distinct, and duplicate values.
4. Streamline the data migration validation strategy across teams
Developing effective validation strategies for all stages of migration, i.e., pre-migration, during, and post-migration, is key to a successful migration. While these validation strategies are primarily the responsibility of the IT department in a company, they affect most teams, if not the entire organization.
Company-wide alignment on the projected validation checkpoints and timelines is important to ensure that operations are not unexpectedly impacted. It also presents an opportunity to spread awareness about the current data architectures and what the validation protocols plan to improve. Communication with relevant stakeholders in the organization is, thus, vital for the validation plans to be successfully implemented.
Additionally, different types of validation checks that are to be run during the migration process can also be decided here. These could include data consistency and data mapping in the pre-migration validation stage, checking for data integrity and error handling during migration, and conducting data quality assessment in post-migration validation.
It is also important to maintain documentation of the validation process. The feedback from the data migration can be looped in for future migrations and audits and also provides visibility to different teams and departments in the organization.
5. Prepare a robust data backup plan
During the migration process, some data may not be migrated from the old system to the target system owing to compatibility issues or incomplete data transfer. In some cases, it could result in permanent data corruption or loss. To avoid these pitfalls and ensure business continuity, it is essential to have a robust data backup plan in place for the migration process.
Companies can also consider migrating to a pilot environment to resolve any issues. Once the migration flow has been deemed seamless and clear of any data security concerns, it can be shifted to the production environment.
6. Leverage automated data migration validation tools
Organizations can opt for third-party automated validation tools if they don’t have the in-house expertise or if the migration process poses significant compliance risks. These tools offer automated workflows for validating vast volumes of data and ensuring data integrity and accuracy in the migrated datasets.
For instance, Telmai provides centralized observability throughout the migration process with protocols for auditing and validation. By leveraging such tools, companies can ensure cost-efficient migrations without encountering the risks associated with manual validation techniques.
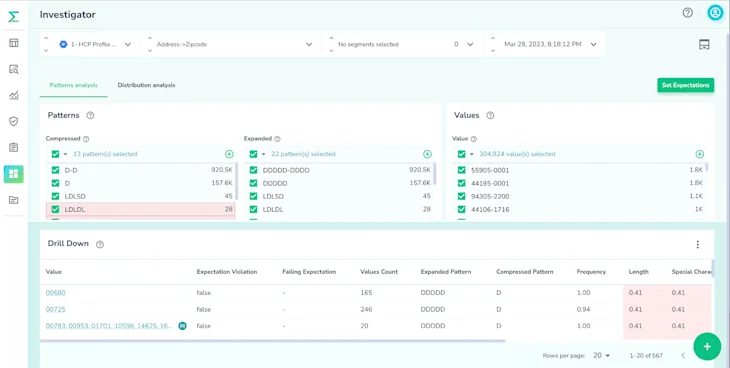
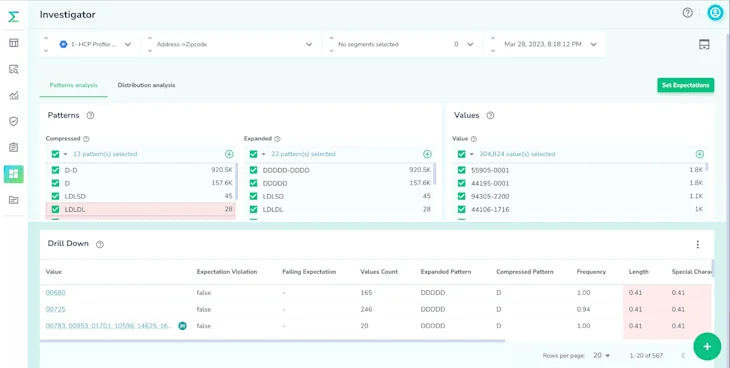
As shown above, Telmai can conduct pattern analysis on regex and expanded patterns as well as distribution analysis on the distribution of data.
7. Execute post-migration validation workflows
Post-migration validation is a critical step in the data migration journey as it helps verify the completeness and accuracy of the shifted data. Data reconciliation is a verification technique that is usually employed here. It proactively compares the source and target datasets and points out any discrepancies.
By reconciling the data in both systems, it can be ensured that the data transfer was adequately completed without any data loss or breach and that the migration success criteria were met. Therefore, thorough post-migration validation is essential because it guarantees an error-free transition and business continuity.

Using Telmai, you can measure the observed accuracy and completeness of the data with the estimated thresholds. This helps in continuous monitoring and in efficiently resolving issues related to data quality. Telmai also assists in diagnosing relative and absolute drift across different dimensions so they can be corrected in real-time.
8. Establish effective post-migration monitoring & evaluation protocols
Continuous monitoring and evaluation of the target system after the transition is also considered a significant data migration best practice. Establishing monitoring protocols to evaluate the new system’s reliability and ensure early diagnosis of performance issues is imperative. Moreover, companies can optimize the system’s performance at this stage by using feedback from the migration process.

Additionally, companies should consider developing data governance policies for the new system to ensure compliance with regulatory requirements. This would help preserve data integrity and make monitoring and evaluation of the new system much more manageable and cost-effective.
Final thoughts
In conclusion, data migration validation is an essential process that companies must undergo to ensure the success of their migration projects. By embracing the data migration validation best practices outlined above, businesses can enhance their operations and protect their data assets and architecture.
It is imperative for organizations to employ the right data migration validation tools. Telmai offers state-of-the-art data migration validation solutions that are crucial for ensuring the success of data migration projects. Aside from offering automated profiling and validation, Telmai can track data migration metrics, eliminate infrastructural overheads, and offer post-migration observability. It also provides alerts on data drifts and identifies their root causes and potential resolutions in real-time.
You can request a demo or contact us here to resolve your data migration validation needs.
Passionate about data quality? Get expert insights and guides delivered straight to your inbox – click here to subscribe to our newsletter now.
- On this page
See what’s possible with Telmai
Request a demo to see the full power of Telmai’s data observability tool for yourself.